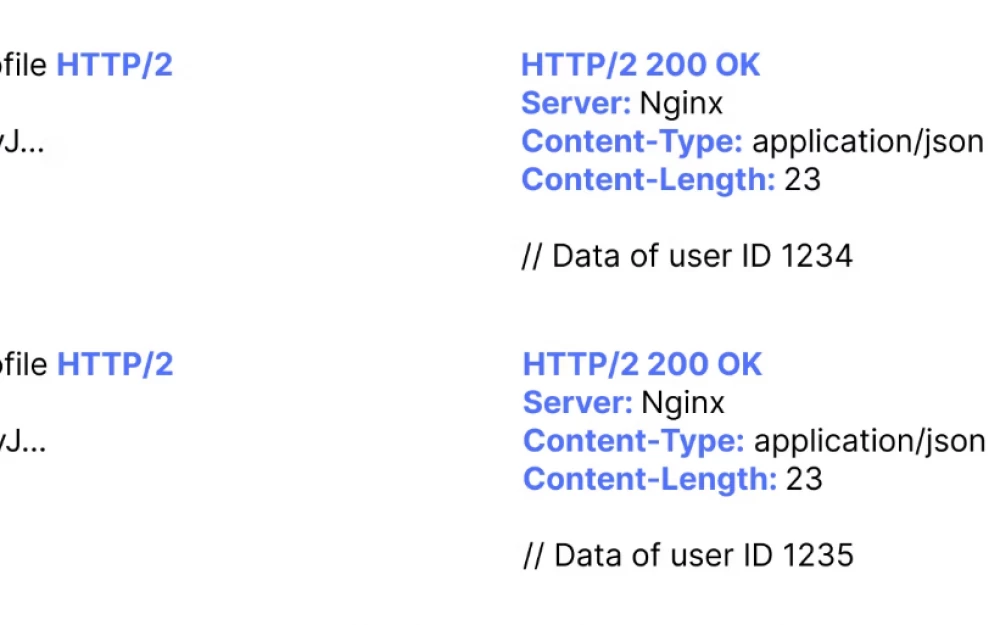
According to the tag exploitation, the following results have been found:
IDOR: A Complete Guide to Advanced Exploitation of IDOR Vulnerabilities
IDOR vulnerabilities are among the most common security vulnerabilities in modern web applications and APIs. It is not surprising that they are often recommended to novice vulnerability hunters, as they are easy to find and exploit, and by their nature, they are high-severity vulnerabilities.