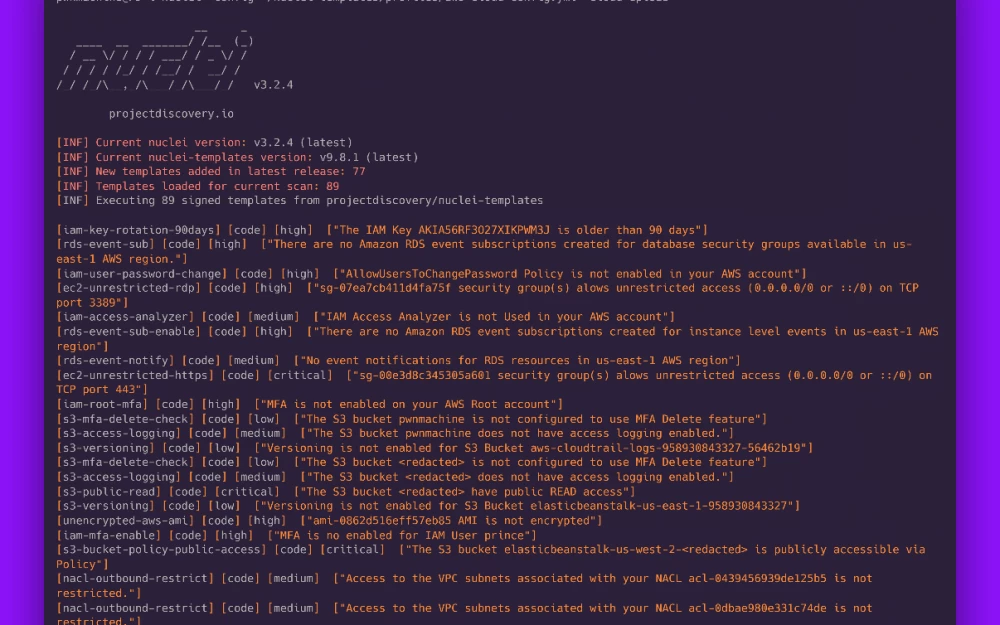
How to find both the goblin and the rat. Interview with researchers from the Solar Group who discovered the GoblinRAT malware
The tekkix news service visited the SOC Forum 2024. This is another event dedicated to cybersecurity, organized by the Solar Group of companies. Due to a busy work schedule,…